Description
If you sell a WordPress plugin or theme to anyone in the EU, the EU Cyber Resilience Act (Regulation 2024/2847) applies to you. It does not matter where you are based or whether your product is free. Agencies distributing custom plugins or themes to EU clients are also in scope.
From September 11, 2026, you need a documented vulnerability reporting process, the required security documents, and a way to monitor your products for known vulnerabilities. ResilienceWP is built for WordPress developers — plugin developers, theme developers, and agencies — to cover all of that in one place.
Non-compliance carries fines up to EUR 15 million or 2.5% of global annual turnover. Authorities can also force non-compliant products off the EU market.
The free plan covers the paperwork side of compliance: checklist, five document templates, and the CRA education guide. Paid plans add automated vulnerability scanning, email alerts, the Incident Center for ENISA notification management, and downloadable compliance reports, all directly inside your WordPress admin. Pro plans also include webhook integrations for CI/CD pipelines and external tools — get real-time notifications when scans complete or vulnerabilities are found.
For pricing, documentation, and more details visit resiliencewp.com.
Compliance Checklist (Free)
26 actionable items, each mapped to a specific CRA article. Five categories cover everything the regulation requires:
- Risk Assessment: documenting threats, attack surfaces, and mitigations
- Secure Development: secure defaults, no known exploitable vulnerabilities at release
- Vulnerability Handling: disclosure policy, coordinated reporting, user notification
- Required Documentation: SBOM, Declaration of Conformity, technical file
- Post-Market Obligations: ongoing monitoring, security updates, end-of-life policy
Every item has a plain-English explanation of what it means and why it matters. Check items off as you complete them. Progress saves automatically.
Document Generator (Free)
Generate the five documents the CRA requires before you can legally place a product on the EU market:
- Vulnerability Disclosure Policy (Article 13(6)): your public process for receiving and handling security reports from researchers
- Incident Response Plan: your internal procedure when a vulnerability is discovered or actively exploited
- EU Declaration of Conformity: the formal self-declaration that your product meets CRA essential requirements
- Software Bill of Materials (SBOM) (Article 13): a structured inventory of your plugin’s components, dependencies, and third-party libraries
- security.txt: the machine-readable contact file security researchers use to reach you, placed at /.well-known/security.txt
Fill in your plugin name, contact details, and a few specifics. Download in text or markdown format. No starting from scratch, no lawyer needed for the first draft.
CRA Education Centre (Free)
An article-by-article breakdown of Regulation (EU) 2024/2847, written for developers rather than legal teams. Understand what each obligation actually requires: what counts as “active exploitation,” what an SBOM needs to contain, what the 24-hour reporting window really means.
Vulnerability Scanner (Basic and Pro)
Connect your account to ResilienceWP and it monitors your plugins against the WPScan vulnerability database on a regular schedule. Weekly on Basic, daily on Pro.
You can monitor any plugin by its WordPress.org slug, not just the plugins currently installed on your site. If your plugin depends on WooCommerce, ACF, or any other third-party plugin, you can add those slugs directly and track vulnerabilities in your dependencies. Plugins can also be added directly from your installed plugins list.
The moment a new vulnerability is found, you get an email with the severity rating, CVE ID, affected version range, and fix version if one is available. Back in your WordPress admin, vulnerabilities are grouped by plugin and sorted by date discovered, so you can see at a glance which plugins have open issues and how old they are.
Each vulnerability card shows:
- Severity (Critical / High / Medium / Low / Info) with colour coding
- CVE identifier linked directly to the NVD entry
- The fix version (or “no fix available yet”)
- An action hint: whether to update, acknowledge, or open an incident
- A button to report the incident directly to the Incident Center
Status tracking lets you mark vulnerabilities as Open, Acknowledged, In Progress, Resolved, or False Positive. Export the full vulnerability list as CSV for your compliance records.
Incident Center (Basic and Pro)
When a vulnerability in your plugin is being actively exploited, the CRA requires you to notify ENISA within 24 hours. The Incident Center tracks that deadline from the moment you log first awareness and guides you through the complete regulatory workflow.
Creating a new incident logs the discovery timestamp and starts all three countdown timers simultaneously:
- Early Warning: due within 24 hours of first awareness
- Vulnerability Notification: due within 72 hours, with full technical details
- Final Report: due within 14 days, including root cause and remediation steps
The case view shows:
- Live countdown timers for each notification deadline, turning amber at 6 hours and red when overdue
- A completeness score on your incident report so you know exactly what information is still missing
- A “Where to Submit” section with direct links to ENISA’s reporting portal, the EU CSIRT network directory, and the CVE Programme at MITRE
- A full audit log recording every action taken, every field updated, and every notification submitted
On Pro, you can export the full incident case including all notifications and the complete audit log, formatted for submission to regulators or for your compliance archive.
Dashboard and Compliance Score
The dashboard gives you a live compliance score (0-100) with a transparent breakdown:
- -15 points per open critical vulnerability
- -7 points per open high vulnerability
- -3 points per open medium vulnerability
- -20 points per overdue incident (past the 24-hour ENISA deadline)
- -5 points per active open incident
It is not a vanity metric. It is a working indicator of where you stand against your CRA obligations at any point in time, with the exact deductions shown so you know what to fix first.
Compliance Reports and SBOM Export (Basic and Pro)
Generate a PDF compliance report for auditors or regulators covering your vulnerability history, resolution timeline, and document status. Export your Software Bill of Materials in standard format, as required by CRA Article 13.
Webhook Integrations (Pro)
Connect ResilienceWP to your CI/CD pipeline, Slack, or any external tool with webhook callbacks. Configure webhook endpoints in Settings and receive real-time HTTP POST notifications with HMAC-SHA256 signed payloads when:
- A scheduled or manual scan completes
- A new vulnerability is found in one of your monitored plugins
Each webhook delivery is logged with status codes and response data, so you can debug integration issues directly from your WordPress admin. Manage up to 5 webhook endpoints per account, toggle them on and off, and filter by event type.
Who needs to comply
- Commercial plugin developers: selling to EU customers through any channel (your site, Envato, direct) makes you the manufacturer under the CRA
- WordPress agencies: distributing custom-built plugins to EU clients, even for a single client, counts as placing a product on the market
- Freemium developers: having a free version does not exempt you; any commercial activity tied to the product brings you in scope
- Theme developers: themes with shortcodes, API integrations, or custom post types may qualify as “products with digital elements”
Key dates
- 10 December 2024: CRA entered into force. Transition period began.
- 11 September 2026: Vulnerability and incident reporting obligations apply.
- 11 December 2027: Full CRA application. All requirements in effect.
Source Code
The admin dashboard is built with React and compiled using Vite. The uncompiled source is included in the plugin ZIP under admin/src/. To rebuild from source:
- Install Node.js 20+ and pnpm 10+
- Run
pnpm installin the plugin directory - Run
pnpm buildto recompile the admin dashboard
External Services
ResilienceWP API (https://api.resiliencewp.com)
Used for API key verification, vulnerability scanning, incident management, and report generation. Data sent: API key, WordPress site URL, plugin slugs and versions.
Terms of Service | Privacy Policy
WPScan (via ResilienceWP API)
Plugin vulnerability data is sourced from the WPScan database. Plugin slugs are sent through the ResilienceWP API. No personal data is sent from your WordPress installation directly to WPScan.
WPScan Terms | WPScan Privacy Policy
Paddle (payments)
Subscription payments are processed by Paddle as merchant of record. Payment data is handled entirely by Paddle and never passes through our servers.
Paddle Terms | Paddle Privacy
Screenshots

Dashboard showing the live compliance score with per-category deduction breakdown, open vulnerabilities summary, and incident status.

Compliance checklist organised into CRA categories, showing article references, plain-English explanations, and a progress bar.

Document generator with the four required CRA documents listed and a generator form open for the Vulnerability Disclosure Policy.

Vulnerability scanner with plugins grouped by name, severity-coded vulnerability cards, CVE IDs, and action hints for CRA obligations.
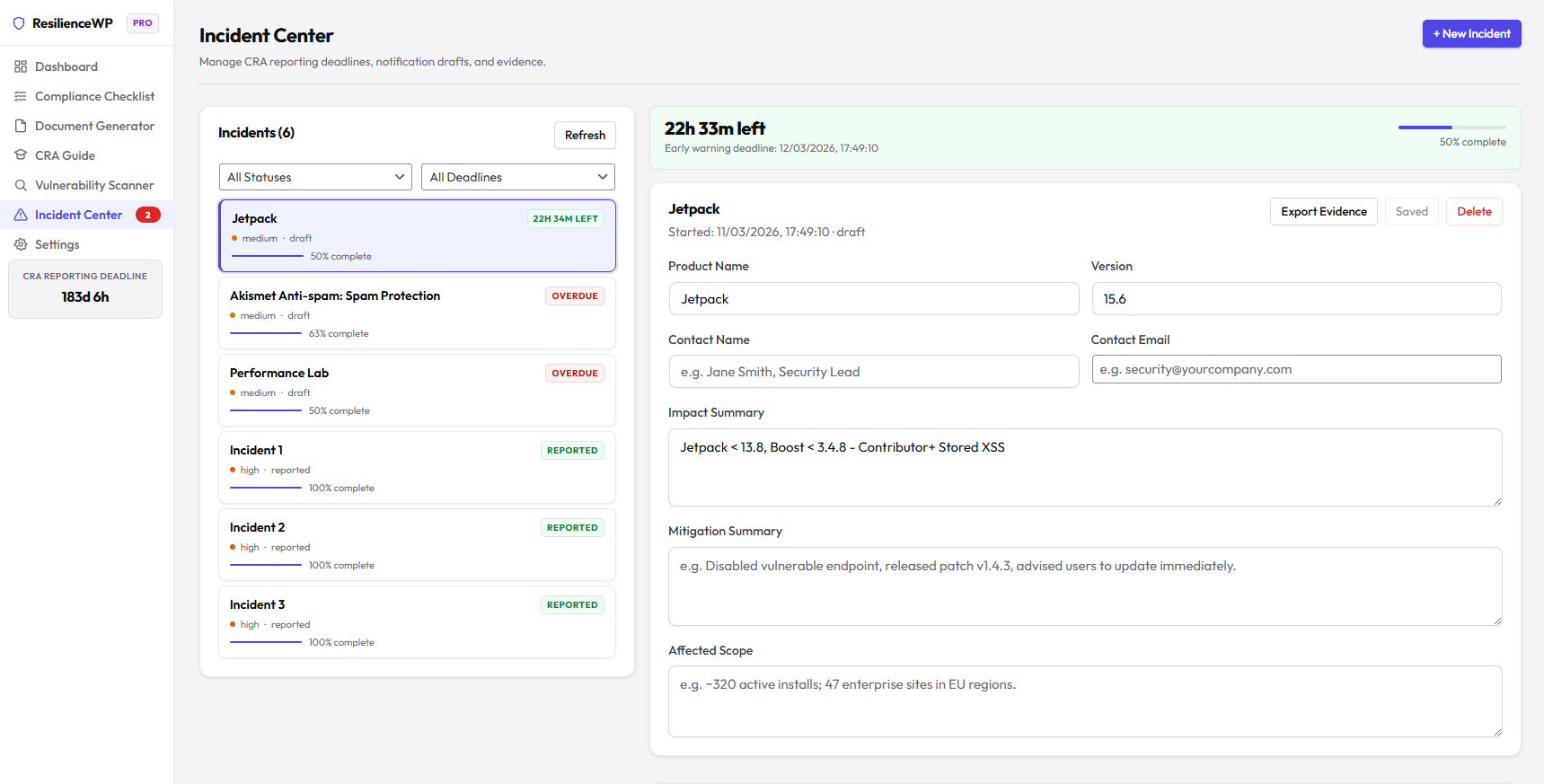
Incident Center showing an active incident case with the 24-hour countdown timer, three-stage notification timeline, completeness score, and authority submission links.

Settings page showing API key entry, connected plan status, site URL configuration, and webhook endpoint management (Pro).
Installation
Getting started (free features, no account needed):
- Go to Plugins > Add New in your WordPress admin and search for “Resilience Compliance Manager”
- Install and activate
- Click ResilienceWP in your admin sidebar
- Start with the Compliance Checklist. No API key or account required.
Enabling vulnerability scanning (paid plans):
- Create an account at resiliencewp.com and subscribe to a plan
- Copy your API key from the welcome email
- Go to ResilienceWP > Settings, paste your API key, and click Verify and Save
- Go to ResilienceWP > Scanner, click Add Plugins, and select the plugins you want to monitor
- Click Scan Now to run your first scan, or wait for the next scheduled scan
FAQ
-
Does the CRA apply to my free WordPress plugin?
-
The test is commercial activity, not whether end users pay. If you run ads on your plugin’s site, accept donations that influence development, offer a paid upgrade (freemium), or bundle the plugin in any paid product or service, the CRA likely applies. Non-commercial open-source software published with no revenue connection is generally exempt, but the line is not always obvious.
-
I’m not based in the EU. Does the CRA apply to me?
-
Yes. The CRA applies to products placed on the EU market, not to developers based there. If EU users can purchase or use your plugin commercially, you’re in scope. Non-EU developers may also need to appoint an authorised representative based in the EU.
-
What’s the minimum I need in place by September 2026?
-
The reporting obligations kick in first on September 11, 2026. You need a working process to detect vulnerabilities in your plugin and report actively exploited ones to ENISA within 24 hours of becoming aware. You also need to notify affected users without undue delay. The ResilienceWP checklist walks you through exactly what that process needs to include.
-
Will this tell me if my plugin has security vulnerabilities?
-
Paid plans run automated scans against the WPScan vulnerability database, the largest database of known WordPress plugin CVEs. ResilienceWP surfaces any known vulnerabilities for the plugins you’re monitoring, including severity, affected versions, and available fixes. It does not perform source code analysis or dynamic penetration testing of your own plugin. For that you’d need a dedicated security audit.
-
What documents does the CRA require?
-
You need: a risk assessment, a coordinated vulnerability disclosure policy, a Software Bill of Materials (SBOM), an EU Declaration of Conformity, and technical documentation of your security measures. The ResilienceWP document generator produces drafts for all of these. Fill in your details and download.
-
Is ResilienceWP a substitute for legal advice?
-
No. ResilienceWP is a compliance assistance tool. The checklist and documents are designed to help you understand and implement your obligations, not to constitute legal advice. Consult a qualified legal professional for advice specific to your situation.
-
What happens to my data if I delete the plugin?
-
Checklist progress and generated documents are stored in your own WordPress database. Deleting the plugin via the WordPress admin removes all local data. Vulnerability and incident data in our systems is handled per our privacy policy and can be requested for deletion by contacting support@resiliencewp.com.
-
Does this work with WordPress Multisite?
-
Standard WordPress installations are fully supported. Multisite support is planned for a future release.
Reviews
There are no reviews for this plugin.
Contributors & Developers
“Resilience Compliance Manager” is open source software. The following people have contributed to this plugin.
ContributorsTranslate “Resilience Compliance Manager” into your language.
Interested in development?
Browse the code, check out the SVN repository, or subscribe to the development log by RSS.
Changelog
1.2.12
- Updated screenshots and banner assets.
- Refined admin UI typography and design alignment.
- Added website link to plugin description.
1.2.11
- Moved CRA reporting countdown to sit below Settings in the admin sidebar.
1.2.8
- Internal webhook routing refactor and admin UI tweaks. No functional changes for end users; safe maintenance release.
1.2.7
- Added webhook integrations for Pro plan: configure up to 5 webhook endpoints to receive real-time HTTP POST notifications when scans complete or vulnerabilities are found. Payloads are signed with HMAC-SHA256 when a secret is configured. Delivery history with status codes is visible in Settings.
1.2.4
- Increased plan limits: Basic now monitors up to 5 plugins (was 3); Pro now monitors up to 20 plugins (was 10).
- Broadened product scope: all copy updated to reflect that the CRA applies to WordPress plugin developers, theme developers, and agencies — not just plugin developers.
1.2.3
- Fixed CycloneDX JSON download failing in non-HTTPS WordPress admin environments: replaced
crypto.randomUUID()(requires secure context) with a compatible Math.random-based UUID generator that works over HTTP. - Removed founding member promotional banner from the web pricing page.
- Overhauled admin UI with a refined indigo design system: updated primary color palette, shadow scale, larger border radii, card hover effects, frosted-glass header, pill-shaped badges, and improved typography using Outfit and DM Mono fonts.
- Improved plugin navigation: Settings moved to a dedicated footer area in the sidebar; Quick Actions and Category Progress now display side-by-side on the Dashboard for a cleaner layout.
1.2.2
- Added CycloneDX 1.5 JSON SBOM download to the Document Generator: the SBOM template now has a “Download CycloneDX JSON” button that generates a machine-readable SBOM compatible with OWASP Dependency-Track, GitHub, and other tooling — in addition to the existing human-readable text output.
1.2.1
- Added PDF Compliance Report template (Pro): a structured point-in-time report covering plugin portfolio, open vulnerabilities, and incident history — for demonstrating CRA compliance to customers, auditors, or enterprise buyers.
- Document Generator now shows a Pro badge on premium-only templates with a direct link to upgrade for non-Pro users.
- Fixed feature table column header alignment on the Dashboard upgrade card.
- Fixed button hover text color across the admin UI.
1.2.0
- Added checklist evidence notes: each checklist item now has an Evidence / Notes field (expands under “More”) where you can record links, references, or explanations of how you completed the item. Notes save automatically with debouncing.
- Added Document Generator links in checklist: items for VDP, security.txt, Incident Response Plan, Declaration of Conformity, and SBOM now have a direct “Generate…” button to the Document Generator.
- Added compliance score breakdown on the Dashboard: paid users can expand a “See score deductions” panel on the score card showing exactly which vulnerabilities and incidents are reducing their score and by how much.
- Added bulk vulnerability actions in Scanner: a select-all checkbox and bulk Acknowledge / Mark Resolved buttons let you process multiple vulnerabilities at once.
- Added version mismatch warning in Scanner: if a monitored plugin’s recorded version differs from the installed version, a warning is shown on the plugin row so you know scanning may be against the wrong version.
- Added WordPress.org review nudge: free users who have completed 50%+ of their checklist after 30+ days are shown a dismissable prompt to leave a review.
1.1.0
- Added delete incident: incidents can now be permanently removed from the Incident Center with a confirmation dialog
- Added Pro-only gate for Evidence Export: Basic plan users see a clear upgrade prompt; Pro users retain full export functionality
- Replaced all browser alert() and confirm() dialogs with native in-app confirm dialogs and toast notifications
- Improved notifications across Document Generator (save/delete), Vulnerability Scanner (remove plugin), and Incident Center
- Incident Center toast confirms deletion and all other state changes without blocking the page
1.0.1
- Fixed checklist progress not persisting across page refreshes, caused by a WordPress dbDelta table creation issue
- Added database error handling with a user-facing message if a checklist item fails to save
- Improved database schema versioning so tables are correctly rebuilt when the plugin updates
1.0.0
- Initial release
- 26-item CRA compliance checklist mapped to regulation articles
- Document generator: Vulnerability Disclosure Policy, Incident Response Plan, EU Declaration of Conformity, security.txt
- CRA Education Centre with article-by-article breakdown
- Vulnerability scanner powered by WPScan (Basic and Pro plans)
- Incident Center with 24-hour ENISA deadline tracker and three-stage notification workflow (Basic and Pro)
- Live compliance score dashboard with per-category deduction breakdown
- SBOM export in standard format per CRA Article 13 (Basic and Pro)
- PDF compliance report generation for auditors (Basic and Pro)
- Email alerts for new vulnerability discoveries (Basic and Pro)
- Vulnerability grouping by plugin, sorted by date discovered
- CVE IDs linked to NVD for full vulnerability detail
